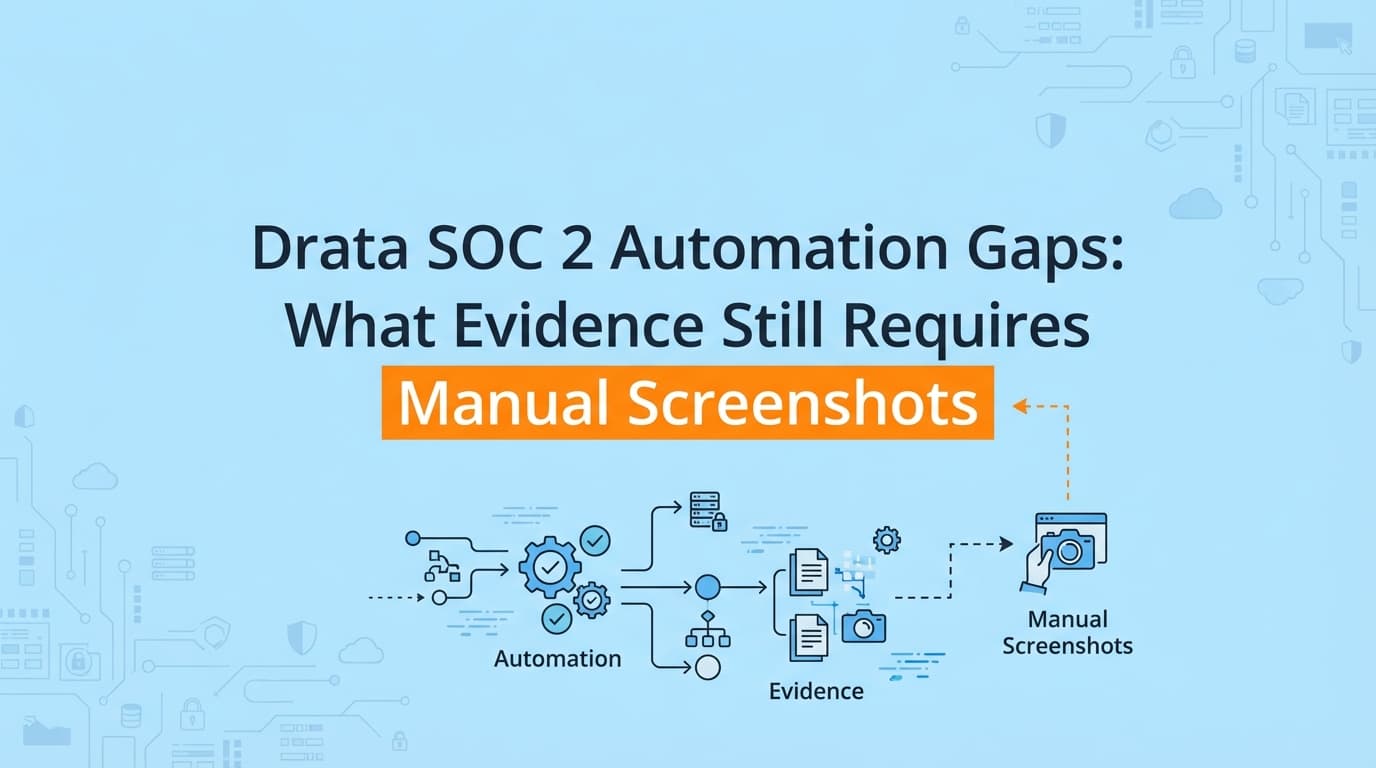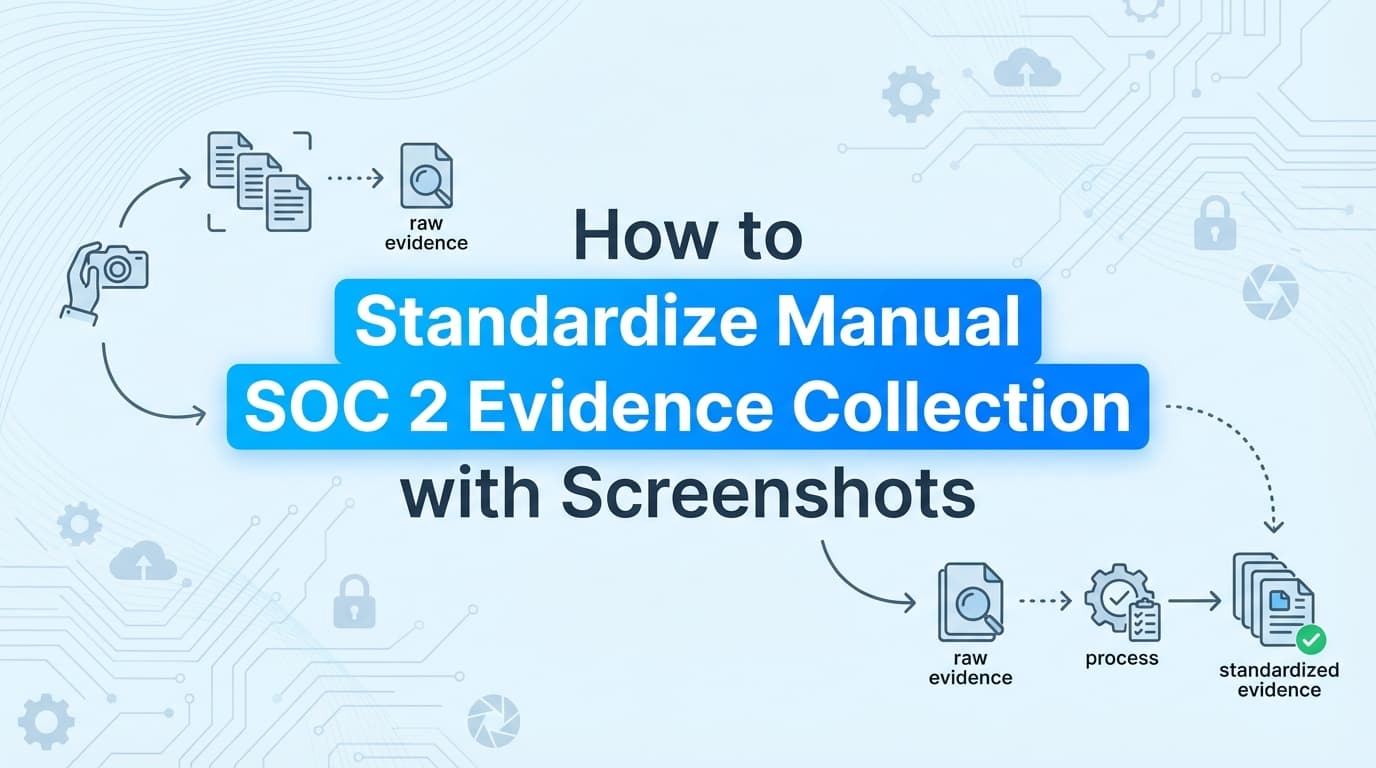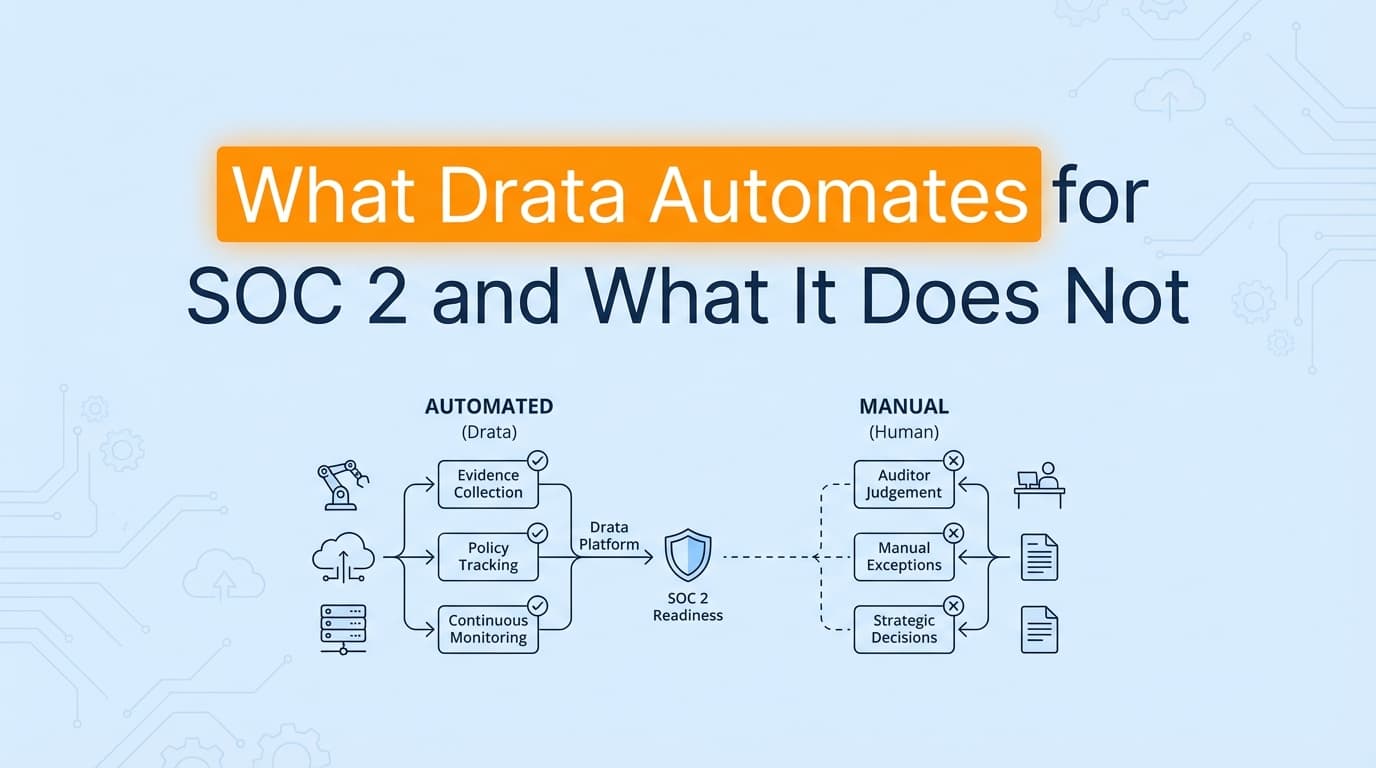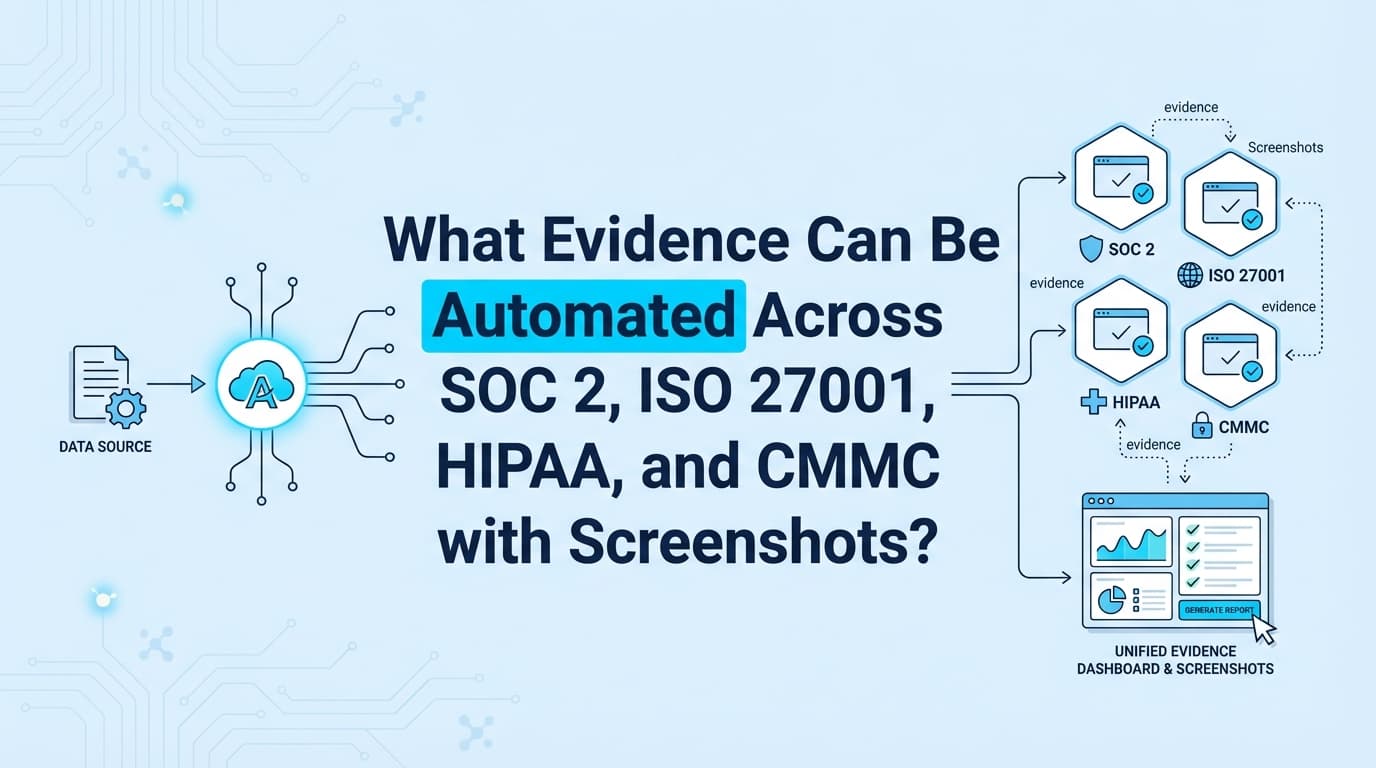
What Evidence Can Be Automated Across SOC 2, ISO 27001, HIPAA, and CMMC with Screenshots?
Yes. You can now automate evidence collection for access controls, change management, and application workflows across SOC 2, ISO 27001, HIPAA, and CMMC. This article details the specific evidence types that AI tools capture via screenshots and APIs to replace manual audit work.