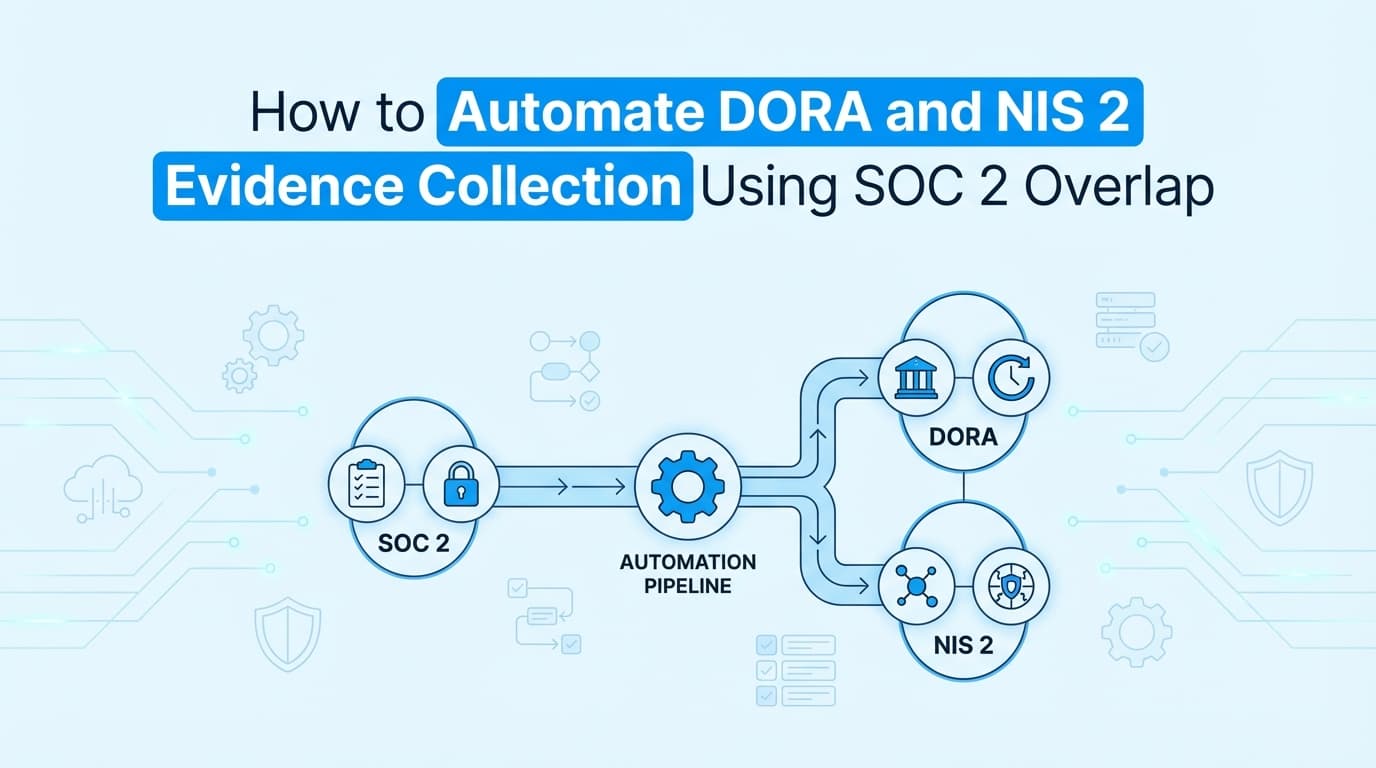
How to Automate DORA and NIS 2 Evidence Collection Using SOC 2 Overlap
DORA and NIS 2 compliance require strict proof of operational resilience that goes beyond standard SOC 2 policies. This guide explains how to map your existing SOC 2 controls to EU cybersecurity regulations and automate the visual evidence collection required for incident response and third-party risk management.
If you sell software in Europe, you are likely buried in the alphabet soup of EU cybersecurity regulations. Between DORA compliance for financial entities and NIS 2 compliance for critical infrastructure, it feels like you need to build a massive new compliance program from scratch.
You don't. Your existing SOC 2 program already covers the foundational policies.
The actual gap between SOC 2 and these EU regulations is in the evidence. While SOC 2 accepts policy documentation and configuration checks, DORA requires continuous proof of operational resilience. Automating DORA and NIS 2 evidence collection means capturing screenshots of actual disaster recovery tests, incident response workflows, and third-party vendor dashboards.
Here is how to map what you already have and automate the evidence collection for what you are missing.
What Is the Actual Difference Between DORA, NIS 2, and SOC 2?
SOC 2 is an audit framework focused on data security and privacy, while DORA and NIS 2 are legal mandates focused on operational resilience and incident reporting.
Honestly, most teams overthink the differences in the policies themselves. The controls are largely the same. The difference lies in what the auditor or regulator expects you to prove.
| Framework | Primary Focus | Evidence Expectation | Overlap Level |
|---|---|---|---|
| SOC 2 | Service organization trust (US-centric) | Proof of configuration and process adherence over a specific period. | Baseline for both. |
| DORA | Financial sector & ICT providers | Proof of continuous operational resilience and deep vendor monitoring. | High overlap with CC7 and CC9. |
| NIS 2 | Critical infrastructure (EU-wide) | Proof of rapid incident detection, reporting, and supply chain security. | High overlap with CC7.3. |
Where Does SOC 2 Evidence Fall Short for DORA Compliance?
SOC 2 evidence often acts as a snapshot. You provide a screenshot showing that your backup policy is configured correctly or that AWS RDS automated backups are enabled.
DORA does not just care that the backup exists. It requires proof that the system actually works when it breaks. This is the concept of operational resilience.
For DORA compliance, you need visual evidence of the recovery process in action. This means capturing screenshots of a restored database timestamp, the success message of a failover test, or the specific Jira workflow where your engineering team documented a tabletop disaster recovery exercise. Configuration data pulled from an API is not enough to prove resilience.
How Do You Map SOC 2 Controls to DORA and NIS 2 Requirements?
You do not need to rewrite your security program. You just need to map your existing SOC 2 Trust Services Criteria to the specific articles in the EU directives.
ICT Risk Management (DORA Art. 5-15) vs. SOC 2 CC6 and CC7 Your logical access controls (CC6.1) and system operations (CC7.2) map directly to DORA's risk management requirements. You already enforce MFA, role-based access, and network segmentation. The evidence remains the same: screenshots of your identity provider configurations, firewall rules, and quarterly access reviews.
Incident Reporting (NIS 2 Art. 23) vs. SOC 2 CC7.3 This is where the rigor increases. SOC 2 requires you to have an incident response plan. NIS 2 requires you to issue an early warning report within 24 hours of a significant incident. To prove compliance, you need evidence showing the exact timeline of detection, triage, and reporting. Workflow recordings of your incident response process in Jira or PagerDuty, complete with timestamps, are critical here.
Digital Operational Resilience Testing (DORA Art. 24) vs. SOC 2 CC9 SOC 2 asks how you identify and mitigate risks. DORA Article 24 demands specific, documented operational resilience testing. You must provide evidence of vulnerability assessments, open-source software checks, and full-scale penetration tests, alongside the visual proof that remediation steps were actually implemented in your codebase or infrastructure.
What Specific Screenshots Prove Operational Resilience Testing?
Auditors evaluating EU cybersecurity mandates look for specific visual artifacts that prove your systems can withstand and recover from disruptions.
When collecting evidence for operational resilience, ensure you capture:
- Failover execution: Screenshots from your AWS or GCP console showing the exact time a secondary region took over during a simulated outage.
- Incident timelines: Timestamped Slack threads or Jira tickets showing the exact minute an alert fired and when an engineer acknowledged it.
- Restoration validation: Visual proof of a restored database or application state, including the system clock, to prove recovery time objectives (RTO) were met.
- MFA enforcement during anomalies: Screenshots showing access denied messages when a user attempts to log in from an unauthorized IP address during a penetration test.
How Can I Automate ICT Third-Party Risk Management Evidence?
Managing third-party risk is the hardest part of DORA. Article 28 requires you to actively monitor the performance and security of your critical Information and Communication Technology (ICT) providers.
Sending a security questionnaire once a year satisfies SOC 2 CC9.2. It will fail a DORA assessment.
You must prove that you are actively monitoring your vendors. Since you cannot install an agent on your vendor's servers, this evidence is entirely visual. You can automate this by deploying AI agents to regularly capture screenshots of your vendors' public status pages, service level agreement (SLA) dashboards, and your own admin panels showing restricted access configurations for third-party contractors.
Where Traditional GRC Automation Stops for EU Cybersecurity
Traditional GRC platforms like Drata and Vanta are excellent for the policy side of NIS 2 and DORA. They connect to your cloud APIs, verify that encryption is enabled, and check that your employee background checks are complete.
But API-based automation stops where operational resilience begins.
APIs can verify a setting is toggled on. They cannot capture the visual workflow of a disaster recovery test. They cannot document the manual steps an engineer takes in a custom internal admin panel during an incident. They cannot take screenshots of a third-party vendor's SLA dashboard.
Screenata fills this evidence gap. Instead of relying solely on APIs, Screenata uses AI agents to navigate user interfaces, execute test steps, and capture the exact visual evidence required for DORA and NIS 2. It takes the manual screenshot collection that used to consume weeks of engineering time and fully automates it, generating audit-ready PDF packs that prove your systems actually work.
Learn More About SOC 2 Evidence Automation
For a complete look at how to build a scalable evidence collection process, see our guide on automating SOC 2 evidence collection, including how to bridge the gap between API monitoring and the visual proof required by complex regulatory frameworks.
Ready to Automate Your Compliance?
See what your compliance program looks like with your real systems.