What's the Best Way to Generate SOC 2 Control Evidence Automatically from App Workflows?
Install a browser extension that records your application workflows, automatically captures screenshots at each step, and uses AI to generate evidence descriptions mapped to SOC 2 controls (CC6.1, CC6.2, etc.). This approach reduces documentation time by 93%.
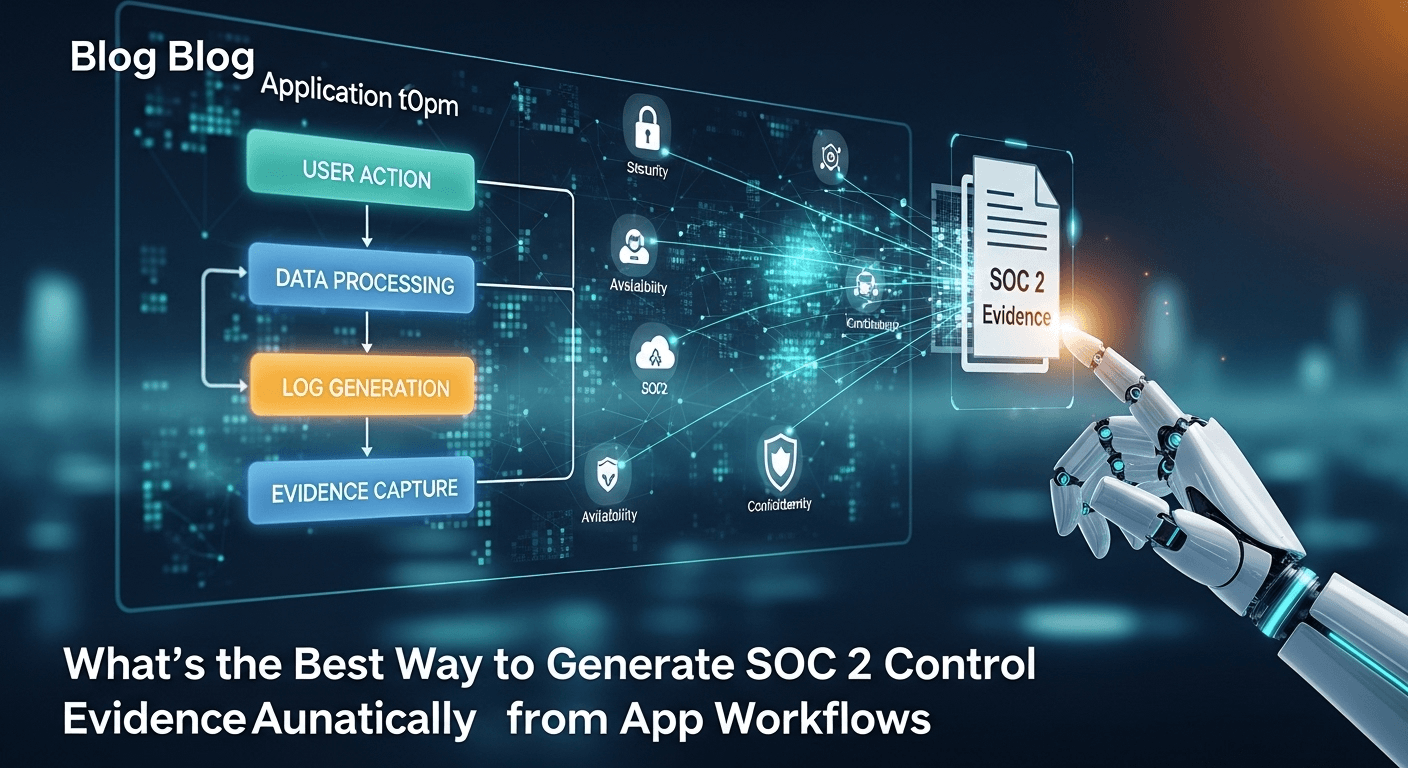
Install a browser extension that records your application workflows, automatically captures screenshots at each step, and uses AI to generate evidence descriptions mapped to SOC 2 controls (CC6.1, CC6.2, etc.). This approach reduces documentation time by 93%.
Why Workflow Evidence is Required
What is Workflow Evidence?
Workflow evidence documents multi-step processes in your application to prove security controls operate as designed.
Examples:
- Change management workflow (CC7.2): Developer creates PR → Reviewer approves → Tests pass → Deploy
- Access provisioning workflow (CC6.2): New hire request → Manager approval → IT creates account → Access granted
- Incident response workflow (CC7.3): Alert triggered → Engineer investigates → Issue resolved → Post-mortem created
Why Auditors Need Workflow Evidence
Auditors want to see:
- Process exists: Documented steps for critical workflows
- Process followed: Screenshots proving steps were actually executed
- Controls enforced: Approval gates, validations, logging at each step
- Continuous operation: Quarterly evidence showing ongoing compliance
Why API data isn't enough:
- APIs can't capture visual UI elements
- APIs don't show human decision-making
- APIs miss context and intent
- Auditors need human-readable proof
Common Workflows That Need Documentation
| SOC 2 Control | Workflow to Document | Evidence Required |
|---|---|---|
| CC6.1 | User permission changes | Before/after screenshots of permissions |
| CC6.2 | User deprovisioning | Screenshots showing account disabled |
| CC7.2 | Code deployment process | PR approval, test results, deploy logs |
| CC7.3 | Incident response | Alert → Investigation → Resolution |
| CC8.1 | Vulnerability remediation | Scan → Ticket creation → Fix → Rescan |
The Manual Workflow Documentation Problem
Traditional Approach (Per Workflow, Per Quarter)
Step 1: Plan documentation (20 minutes)
- Identify which workflow to document
- List all steps in the workflow
- Determine what screenshots to capture
- Assign person to perform documentation
Step 2: Execute workflow (30-60 minutes)
- Manually click through each step
- Stop to take screenshot at each step
- Rename and organize screenshot files
- Note timestamp for each action
Step 3: Write documentation (45-90 minutes)
- Describe what each screenshot shows
- Explain workflow logic and decisions
- Map to SOC 2 control requirements
- Format with proper headings
Step 4: Create evidence pack (30 minutes)
- Import screenshots into Word/Google Docs
- Add captions and annotations
- Include control ID and test metadata
- Export as PDF
Step 5: Upload to GRC platform (10 minutes)
- Navigate to control in Vanta/Drata
- Upload PDF evidence
- Add test date and tester
- Mark control as tested
Total time per workflow: 2.5-3.5 hours Annual cost (4 quarters, 15 workflows): $60,000-$84,000
Problems with Manual Approach
❌ Time-intensive: 3 hours per workflow × 15 workflows × 4 quarters = 180 hours/year
❌ Interrupts normal work: Must stop and manually screenshot during workflow
❌ Inconsistent quality: Different people document differently
❌ Easy to miss steps: Forgetting to screenshot critical moments
❌ Hard to maintain: Process documentation becomes outdated
The Automated Approach: Browser Extension + AI
How It Works (3 Components)
1. Browser Extension Recording
Captures automatically:
- Every page navigation
- Every button click
- Form submissions
- Dialog boxes and modals
- Error messages
- Loading states
- API responses (in DevTools)
Example recording data:
{
"workflow_recording": {
"workflow_name": "Code Deployment - CC7.2",
"start_time": "2024-01-15T14:00:00Z",
"end_time": "2024-01-15T14:08:30Z",
"tester": "engineer@company.com",
"steps": [
{
"step_number": 1,
"timestamp": "2024-01-15T14:00:15Z",
"action_type": "click",
"element": "Create Pull Request button",
"url": "https://github.com/company/repo",
"screenshot": "01_create_pr.png",
"page_title": "company/repo: New Pull Request"
},
{
"step_number": 2,
"timestamp": "2024-01-15T14:02:30Z",
"action_type": "form_submit",
"form_data": {
"title": "Fix user authentication bug",
"description": "...",
"reviewers": ["senior-engineer@company.com"]
},
"screenshot": "02_pr_details.png"
},
{
"step_number": 3,
"timestamp": "2024-01-15T14:05:00Z",
"action_type": "approval",
"approver": "senior-engineer@company.com",
"approval_comment": "LGTM",
"screenshot": "03_pr_approved.png"
},
{
"step_number": 4,
"timestamp": "2024-01-15T14:06:15Z",
"action_type": "status_check",
"ci_status": "passed",
"tests_passed": "287/287",
"screenshot": "04_tests_passed.png"
},
{
"step_number": 5,
"timestamp": "2024-01-15T14:08:00Z",
"action_type": "deployment",
"deploy_method": "Merge and deploy",
"environment": "production",
"screenshot": "05_deployed.png"
}
]
}
}
2. AI Documentation Generation
AI analyzes screenshots and generates:
Step descriptions:
"At 14:00:15 UTC, engineer@company.com initiated a pull request on GitHub repository company/repo. The PR titled 'Fix user authentication bug' included code changes to the authentication module and requested review from senior-engineer@company.com."
"At 14:05:00 UTC, senior-engineer@company.com approved the pull request with comment 'LGTM' (Looks Good To Me), satisfying the required code review control."
"At 14:06:15 UTC, automated CI/CD pipeline completed with all 287 tests passing, meeting the automated testing requirement before deployment."
"At 14:08:00 UTC, the approved and tested code was deployed to production environment via merge-and-deploy workflow."
Control mapping:
{
"control_id": "CC7.2",
"control_name": "Change Management",
"requirements_met": [
"Code review by authorized personnel",
"Automated testing before deployment",
"Approval gates enforced",
"Deployment logged with timestamp and actor"
],
"test_result": "PASS",
"evidence_quality_score": 95
}
3. Audit-Ready Report Generation
Automatically creates:
-
Executive Summary
- Control tested: CC7.2 Change Management
- Workflow documented: Code Deployment Process
- Test date: 2024-01-15
- Result: PASS
-
Workflow Diagram
Create PR → Code Review → Automated Tests → Approval → Deploy (2 min) (3 min) (1 min) (1 min) (2 min) -
Step-by-Step Evidence
- 5 screenshots with AI descriptions
- Timestamps for each step
- Key decision points highlighted
-
Control Verification
- ✅ Code review required and performed
- ✅ Tests must pass before merge
- ✅ Approval by authorized reviewer
- ✅ All changes logged in GitHub audit
-
Appendix
- Raw workflow data (JSON)
- Test metadata
- Compliance certification
Output format: PDF, ready for auditor review
Implementation Guide
Phase 1: Setup (One-Time, 30 minutes)
Step 1: Install Browser Extension (3 minutes)
- Install Screenata from Chrome Web Store
- Login with your account
- Grant necessary permissions:
- Screenshot capture
- Navigation tracking
- Form data recording (optional, for detailed logs)
Step 2: Configure Workflow Templates (15 minutes)
Define workflows to document:
{
"workflows": [
{
"workflow_id": "deployment",
"name": "Code Deployment Process",
"control": "CC7.2",
"frequency": "per_deployment",
"trigger": "url_pattern",
"url_pattern": "github.com/*/pull/*",
"expected_steps": [
"Create PR",
"Code review",
"Tests pass",
"Approve PR",
"Deploy"
],
"min_steps": 4,
"required_elements": [
"reviewer_approval",
"ci_status_success"
]
},
{
"workflow_id": "user_deprovisioning",
"name": "User Account Deactivation",
"control": "CC6.2",
"frequency": "per_termination",
"expected_steps": [
"HR notifies IT",
"IT disables Okta account",
"Verify app access revoked",
"Document in ticket"
]
}
]
}
Step 3: Connect to GRC Platform (10 minutes)
- Navigate to Integrations
- Select Vanta or Drata
- Enter API key
- Map workflow IDs to control IDs
- Test connection
Step 4: Set Recording Preferences (2 minutes)
{
"recording_preferences": {
"screenshot_quality": "high",
"capture_network_requests": true,
"redact_sensitive_data": true,
"redaction_patterns": [
"api_key",
"password",
"ssn",
"credit_card"
],
"auto_start_on_url": [
"github.com",
"app.yourcompany.com"
]
}
}
Phase 2: Recording Workflows (5-10 minutes per workflow)
Example: Recording Code Deployment Workflow
Step 1: Start Recording (15 seconds)
- Navigate to GitHub
- Click Screenata extension
- Select "Code Deployment - CC7.2"
- Click "Start Recording"
- Extension icon turns red (recording active)
Step 2: Execute Normal Workflow (8 minutes)
Just perform your normal deployment process—no need to manually capture screenshots:
-
Create Pull Request (2 min)
- Click "New Pull Request"
- Fill in title and description
- Add reviewers
- Submit
- Extension auto-captures all screens
-
Wait for Review (3 min)
- Reviewer gets notification
- Reviews code
- Leaves approval comment
- Extension captures approval timestamp
-
Verify Tests (1 min)
- CI/CD runs automatically
- Tests complete
- Status checks show green
- Extension captures test results
-
Deploy (2 min)
- Click "Merge Pull Request"
- Confirm deployment
- Verify deployment success
- Extension captures deployment confirmation
Step 3: Stop Recording (10 seconds)
- Click Screenata extension
- Click "Stop Recording"
- Extension shows: "5 steps captured, processing..."
Step 4: AI Processing (60 seconds)
AI automatically:
- Analyzes 5 screenshots
- Generates step descriptions
- Maps to CC7.2 control
- Identifies approval gates
- Verifies all requirements met
- Creates PDF report
Step 5: Review and Export (30 seconds)
- Review PDF preview
- Verify screenshots clear
- Click "Export to Vanta"
- Done!
Total time: 10 minutes (vs 3 hours manual)
Advanced Features
Feature 1: Smart Step Detection
AI detects workflow milestones automatically:
{
"smart_detection": {
"approval_gates": {
"detected": true,
"type": "github_pr_approval",
"approver": "senior-engineer@company.com",
"timestamp": "2024-01-15T14:05:00Z"
},
"test_validation": {
"detected": true,
"type": "ci_status_check",
"result": "success",
"tests_run": 287,
"tests_passed": 287
},
"deployment_confirmation": {
"detected": true,
"environment": "production",
"deploy_method": "github_merge"
}
}
}
Benefits:
- ✅ No need to manually annotate important moments
- ✅ AI highlights critical control points
- ✅ Automatically maps to SOC 2 requirements
Feature 2: Scheduled Workflow Capture
For recurring workflows (quarterly, monthly):
{
"scheduled_captures": [
{
"workflow": "user_access_review",
"control": "CC6.1",
"schedule": "quarterly",
"next_run": "2024-01-15",
"auto_execute": false,
"reminder_days_before": 7,
"assignee": "compliance@company.com"
},
{
"workflow": "vulnerability_scan_review",
"control": "CC8.1",
"schedule": "monthly",
"next_run": "2024-01-15",
"auto_execute": true,
"integration": "tenable_api"
}
]
}
Slack reminder:
🔔 Workflow Evidence Due
Workflow: User Access Review (CC6.1) Due: April 1, 2025 (7 days)
[Record Workflow] [View Template] [Reschedule]
Feature 3: Workflow Comparison
Compare workflows across quarters:
Create PR (2 min) → Review (3 min) → Tests (1 min) → Deploy (2 min)
✅ All controls passed
Create PR (2 min) → Review (SKIPPED) → Tests (1 min) → Deploy (2 min)
⚠️ Missing code review approval
ALERT: Control CC7.2 failed in Q2 - no reviewer approval detected
Benefits:
- Catch control failures immediately
- Ensure consistent process execution
- Track process improvements over time
Workflow-Specific Templates
Template 1: Change Management (CC7.2)
Workflow: Code deployment to production
Required evidence:
- Pull request creation with description
- Code review by authorized person
- Automated test execution and results
- Deployment approval
- Production deployment confirmation
Screenata template:
{
"template": "cc7_2_change_management",
"required_steps": [
{
"step": "pr_creation",
"validation": "url_contains('github.com/pull')",
"screenshot_required": true
},
{
"step": "code_review",
"validation": "element_contains('.review-status', 'approved')",
"required_approvers": 1,
"screenshot_required": true
},
{
"step": "automated_tests",
"validation": "element_contains('.ci-status', 'success')",
"screenshot_required": true
},
{
"step": "deployment",
"validation": "url_contains('deployed')",
"environment_check": "production",
"screenshot_required": true
}
],
"auto_export_on_complete": true,
"vanta_control_id": "CC7.2"
}
Template 2: Access Provisioning (CC6.2)
Workflow: New employee onboarding
Required evidence:
- Access request ticket
- Manager approval
- IT creates accounts (Okta, AWS, GitHub)
- Verification of correct permissions
- Notification to requester
Screenata template:
{
"template": "cc6_2_access_provisioning",
"required_steps": [
{
"step": "access_request",
"validation": "ticket_system_open",
"required_fields": ["requestor", "role", "manager_approval"]
},
{
"step": "okta_account_creation",
"validation": "url_contains('okta.com/admin')",
"verify_user_created": true
},
{
"step": "permission_assignment",
"validation": "role_assigned",
"verify_correct_permissions": true
},
{
"step": "access_verification",
"validation": "user_can_login",
"test_login": true
}
]
}
Template 3: Incident Response (CC7.3)
Workflow: Security incident handling
Required evidence:
- Alert detection
- Incident ticket creation
- Engineer investigation
- Issue resolution
- Post-mortem documentation
Screenata template:
{
"template": "cc7_3_incident_response",
"required_steps": [
{
"step": "alert_detection",
"source": ["pagerduty", "datadog", "cloudwatch"],
"severity_threshold": "high"
},
{
"step": "ticket_creation",
"validation": "jira_incident_ticket",
"required_fields": ["severity", "description", "assigned_to"]
},
{
"step": "investigation",
"capture_logs": true,
"capture_diagnostic_screenshots": true
},
{
"step": "resolution",
"validation": "incident_resolved",
"require_resolution_notes": true
},
{
"step": "post_mortem",
"validation": "document_exists",
"require_root_cause": true
}
]
}
Integration with Existing Tools
GitHub Integration
Automatic workflow detection:
// Screenata detects GitHub workflows automatically
{
"github_integration": {
"detect_pr_workflow": true,
"capture_on_events": [
"pull_request_opened",
"pull_request_approved",
"pull_request_merged"
],
"extract_data": {
"pr_title": true,
"pr_description": true,
"reviewers": true,
"approval_comments": true,
"ci_status": true,
"merge_timestamp": true
}
}
}
Evidence includes:
- PR creation screenshot
- Code review comments
- Approval timestamp
- CI/CD test results
- Merge confirmation
Jira Integration
Ticket-based workflow tracking:
{
"jira_integration": {
"capture_ticket_workflow": true,
"track_status_changes": [
"To Do → In Progress",
"In Progress → Code Review",
"Code Review → Done"
],
"required_fields": [
"assignee",
"reporter",
"priority",
"resolution"
]
}
}
PagerDuty Integration
Incident response workflow:
{
"pagerduty_integration": {
"capture_incident_lifecycle": true,
"track_events": [
"incident_triggered",
"incident_acknowledged",
"incident_resolved"
],
"extract_metadata": {
"severity": true,
"assigned_to": true,
"response_time_minutes": true,
"resolution_time_minutes": true
}
}
}
Comparison: Different Approaches
| Approach | Setup Time | Per-Workflow Time | Annual Hours (15 workflows) | Evidence Quality |
|---|---|---|---|---|
| Manual screenshots | 0 min | 180 min | 360 hours | Medium (inconsistent) |
| Screen recording tools (Loom) | 10 min | 30 min | 63 hours | Low (no structure) |
| RPA (UiPath, Automation Anywhere) | 40 hours | 5 min | 22.5 hours | High (but complex setup) |
| Browser extension + AI | 30 min | 10 min | 30 hours | High (consistent) |
Winner: Browser extension + AI
- ✅ Lowest setup time
- ✅ Best time-to-value ratio
- ✅ High-quality evidence
- ✅ Easiest to maintain
Real-World Success Stories
Case Study 1: SaaS Startup (30 employees)
Challenge: Manual workflow documentation took 4 hours per workflow
Workflows documented:
- Code deployments (CC7.2) - 20/quarter
- User provisioning (CC6.2) - 5/quarter
- Incident response (CC7.3) - 3/quarter
Before automation:
- 28 workflows × 4 hours = 112 hours/quarter
- Annual time: 448 hours
After Screenata:
- 28 workflows × 10 minutes = 4.7 hours/quarter
- Annual time: 18.7 hours
Savings: 429.3 hours annually (96% reduction)
Case Study 2: FinTech (200 employees)
Challenge: Audit failures due to missing workflow evidence
Problem: Manual documentation was skipped during busy periods
Solution: Automated workflow capture with Screenata
Results:
- 100% workflow documentation compliance
- Zero audit findings on workflow evidence
- Passed SOC 2 Type II with no remediation items
- Compliance team reduced from 3 people to 1
Quote:
"We went from missing 30% of workflow evidence to capturing 100%, all while cutting our compliance team size. The browser extension captures everything automatically—no more rushing to screenshot during deployments." - Head of Compliance
Case Study 3: Healthcare SaaS (500 employees)
Challenge: HIPAA + SOC 2 required extensive workflow documentation
Workflows documented:
- PHI access workflows (15 types)
- Incident response (security + privacy)
- Change management (code + infrastructure)
- Access reviews (quarterly)
Before automation:
- 200+ workflow evidence packages per year
- 3 full-time compliance analysts
- 600 hours/year on workflow documentation
After automation:
- Same 200+ workflows documented
- 1 compliance analyst
- 50 hours/year on workflow review
- 550 hours saved
ROI: 350% in first year (including headcount reduction)
Common Mistakes to Avoid
Mistake 1: Not Defining Workflows Clearly
Problem: Recording without clear workflow definition
Result: Missing critical steps, incomplete evidence
Solution: Create workflow templates before recording
Template checklist:
- List all workflow steps
- Define required screenshots
- Identify approval gates
- Map to SOC 2 control
- Set pass/fail criteria
Mistake 2: Recording in Staging Instead of Production
Problem: Auditors want production evidence
Result: Evidence rejected, must re-capture
Solution: Configure templates to require production environment
{
"environment_validation": {
"require_production": true,
"production_indicators": [
"url_contains('app.company.com')",
"!url_contains('staging')",
"!url_contains('dev')"
],
"warning_if_non_production": true
}
}
Mistake 3: Not Redacting Sensitive Data
Problem: PII or credentials visible in screenshots
Result: Security risk, potential compliance violation
Solution: Enable automatic redaction
{
"redaction_rules": [
{
"type": "api_key",
"pattern": "sk_live_[a-zA-Z0-9]{24}",
"replace_with": "sk_live_REDACTED"
},
{
"type": "email",
"pattern": "[a-zA-Z0-9._%+-]+@[a-zA-Z0-9.-]+\\.[a-zA-Z]{2,}",
"replace_with": "***@***.com"
},
{
"type": "ssn",
"pattern": "\\d{3}-\\d{2}-\\d{4}",
"replace_with": "***-**-****"
}
]
}
Mistake 4: Not Scheduling Regular Captures
Problem: Forgetting to capture quarterly evidence
Result: Scrambling before audit, missing evidence
Solution: Set up automated reminders
Recommendation:
- Set calendar reminders for first week of each quarter
- Assign specific workflows to specific team members
- Track completion in dashboard
- Send Slack alerts for overdue workflows
Key Takeaways
✅ Browser extension + AI reduces workflow documentation time by 93% (3 hours → 10 minutes)
✅ Captures screenshots automatically during normal workflow execution
✅ AI generates audit-ready descriptions mapped to SOC 2 controls
✅ Templates ensure consistent evidence across quarters and team members
✅ Integrates with GitHub, Jira, PagerDuty for automatic workflow detection
✅ Annual savings of $60,000-$80,000 for typical SaaS companies with 15 workflows
✅ Higher evidence quality than manual documentation (consistent formatting, no missed steps)
Learn More About SOC 2 Compliance Automation
For a complete guide to automating SOC 2 evidence collection, including how to generate SOC 2 control evidence automatically from app workflows, see our comprehensive SOC 2 automation guide.
Not sure if you even need a compliance consultant? Read Do You Actually Need a vCISO for SOC 2? Probably Not Anymore or The Bootstrapped Founder's Guide to SOC 2.
Ready to Automate Your Compliance?
See what your compliance program looks like with your real systems.